Prevent Identity Thefts
Introduction
Identity theft occurs when someone uses another person's personal identifying information, like their name, user ID or password without their permission, to commit fraud or other crimes.
As we all know, users have the habit of keeping weak passwords. Analysis of hacked passwords shows that large proportions of people keep simple passwords such as ‘12345678’ and ‘passw0rd’, with requirements for alphanumeric passwords scarcely improving the situation. Used in combination with a password, MFA greatly enhances security.
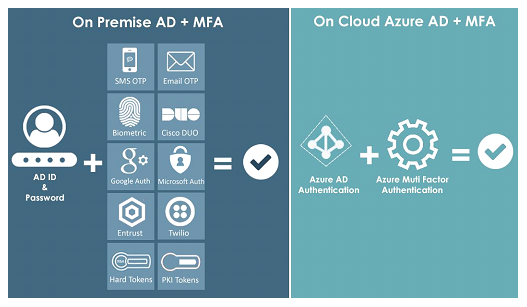
This variety of categories allows for a wide range of authentication techniques and technologies to be used, most of which are far superior to a password. These include sending a pin code to a mobile phone or separate device, adding a biometric key such as a fingerprint, using a code-generating application on a smart phone or computer, or sending the pin by another secure email account.
MFA greatly enhances security and reduces the risk of identity theft.
Multi-Factor Authentication (MFA) is an electronic authentication method in which a user is granted access to a website or application only after successfully presenting two or more pieces of evidence to an authentication mechanism: knowledge & possession. MFA is a core component of a strong Privileged Identity and Access Management (PAM) policy.
Benefits of Multi-Factor Authentication (MFA)
MFA is defined as a security mechanism that requires an individual to provide two or more credentials in order to authenticate their identity. In IT, these credentials take the form of passwords, hardware tokens, numerical codes, biometrics, etc. Using any combination of the examples above is technically MFA, although most implementations leverage two factors, which is why MFA is also known as two-factor authentication(2FA). By leveraging multiple credentials instead of one, the authentication process will remain secure even if one of the authentication factors is compromised. The goal of MFA is to create a layered defense and make it more difficult for an unauthorized person to access a target such as a computing device, network or database. If one factories compromised or broken, the attacker still has at least one more barrier to breach before successfully breaking into the target. For MFA, each additional factor is intended to increase the assurance that an entity involved in some kind of communication or requesting access to some system is who, or what,they are declared to be. The three most common categories are often described as something you know (the knowledge factor), something you have (the possession factor) and something you are (the inherence factor).
Use Cases
Using Multi-Factor Authentication is one way to protect your online accounts against cyber criminals. Multi-Factor Authentication is when you use two or more authentication factors to verify your identify. These factors include:
- Something you know, such as a password, passphrase or personal identification number (PIN)
- Something you have, such as a token or smartcard
- Something you are, such as a biometric like a fingerprint